Your data stays yours. Always.
Complete tenant isolation, full audit trails, UK data residency, and encrypted credentials on every tier. Enterprise-grade security built into the architecture — not bolted on.
Security by architecture, not by policy
Every customer gets their own isolated environment with governed access and complete auditability. Security is structural, not a checklist.
Tenant Isolation
Your data is completely isolated from every other customer. Dedicated environments for warehouse customers, encrypted tenant-scoped access on every tier. No cross-customer data access — ever.
Verified Access
SSO authentication with multi-factor support. Role-based permissions. Session management with idle timeouts. Every request verified.
Full Auditability
Every query, every action, every approval logged with user, timestamp, and context. Nothing happens without a record.
Isolation at every tier
Warehouse customers get dedicated cloud projects. Live Intelligence customers get encrypted, tenant-scoped access with no data stored at rest. Both models enforce complete isolation.
UK Data Residency
All data stored and processed in Google Cloud Platform’s London region. Your data never leaves the UK.
Project-Per-Tenant
Warehouse customers get a dedicated cloud project with isolated storage and compute. Live Intelligence customers query platforms directly — no data stored in our infrastructure.
Encryption
Data encrypted at rest (AES-256) and in transit (TLS 1.2+). HTTPS enforced on every connection.
Credential Security
All platform credentials encrypted at rest with AES-256 and managed through cloud key management. Token refresh handled automatically with encrypted write-back.
Defence at every layer
From authentication through to data access, every layer of the platform is secured independently.
Identity and access management
Industry-standard SSO with multi-factor authentication. Secure session management with idle timeouts. Role-based access controls ensure users only see what they’re authorised for.
- SSO with multi-factor authentication
- Role-based access controls
- Session management with idle timeouts
- Time-limited support access
Defence against common attack vectors
The platform is built with OWASP-aligned security controls at every layer. Injection prevention, cross-site scripting protection, and request forgery defences are structural — not optional.
- Injection prevention on all queries
- Cross-site scripting protection
- Request forgery defences
- Strict input validation and output encoding
Secure by default
All connections are encrypted. Security headers prevent clickjacking, MIME sniffing, and protocol downgrade attacks. Rate limiting protects against abuse.
- HTTPS enforced on all connections
- Security headers (CSP, HSTS, X-Frame-Options)
- Rate limiting on all endpoints
- Outbound request restrictions
Governed data access, not direct database access
Ask Q, Cowork, and portal users all query your data through a governed intelligence layer — never directly against your tables or platform APIs.
Ungoverned access
Qtell governed access
No controls on what queries can run
Destructive operations blocked before execution
A bad query can scan terabytes and cost hundreds
Cost limits enforced before every query runs
Queries can run indefinitely
Automatic timeouts prevent runaway queries
No visibility into what was queried
Every query logged with user and context
AI guesses at metric meanings
Governed definitions for every metric and dimension
The same controls extend to every surface
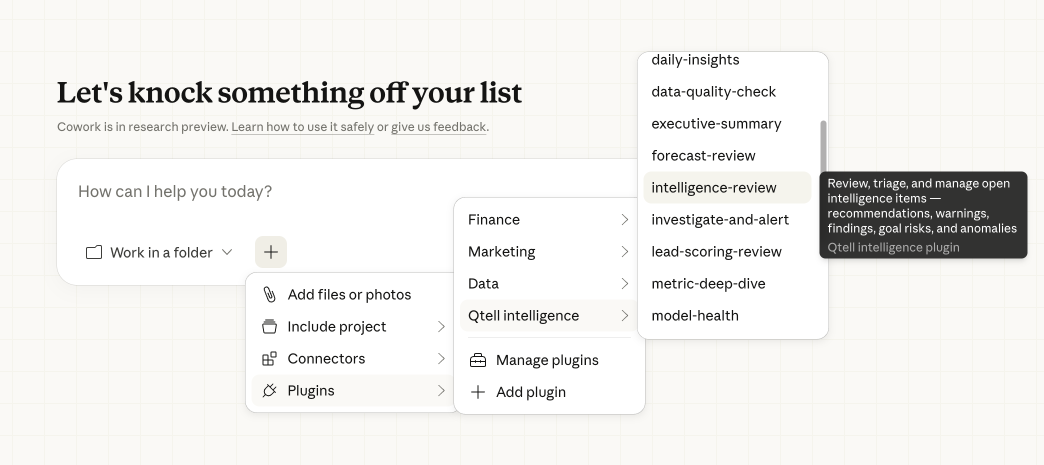
When Cowork or any external integration queries your data, it goes through the same governed access model. Authentication, query governance, and audit trails apply to every request — whether it comes from the portal, the API, or Claude Desktop.
- Authenticated and scoped to your tenant on every request
- Per-tenant data isolation — no cross-customer access
- Every command execution logged with full context
- Rate limiting on all external-facing endpoints
- Same query governance as portal users
Working towards ISO 27001:2022
Qtell is actively pursuing ISO 27001:2022 certification — the international standard for information security management. Our ISMS programme includes formal risk assessment, treatment plans, and a Statement of Applicability.
ISO 27001:2022
Full Information Security Management System in progress. Formal risk assessment, treatment plans, and Statement of Applicability.
GDPR Compliant
UK data residency. Data processing agreements available. Right to deletion supported. No personal data exposed in the analytics layer.
Data Processing Agreements
Standard DPA available for all customers. Custom agreements for enterprise requirements. Supplier DPAs tracked and managed.
Access Control
Role-based access with workspace-level permissions. Users only see data they’re authorised for. Formal access review process.
Security at scale
Cross-customer access
Complete tenant isolation on every product tier
UK data residency
All data stored and processed in GCP London
27001 in progress
Formal ISMS programme with risk assessment and Statement of Applicability
Action logged
Complete audit trail for compliance and governance
Security questions
All data is stored and processed in Google Cloud Platform’s London region. Warehouse Intelligence customers get a dedicated cloud project with isolated storage and compute. Live Intelligence customers connect directly to their platforms — no data is stored in our infrastructure beyond encrypted credentials. Your data never leaves the UK and never mixes with other customers’ data.
We are actively pursuing ISO 27001:2022 certification. Our ISMS programme includes formal risk assessment, treatment plans, and a Statement of Applicability. Our infrastructure runs on Google Cloud Platform, which holds SOC 1, SOC 2, SOC 3, ISO 27001, ISO 27017, and ISO 27018 certifications. We can provide detailed security documentation for your procurement team.
No. All queries — whether from the portal, Cowork, or the API — go through the same governed intelligence layer. Destructive operations are blocked, cost limits are enforced, and every query is logged. This applies to both warehouse queries and live platform connections.
We use industry-standard SSO with multi-factor authentication support. Sessions are managed with secure cookies and idle timeouts. Role-based access controls ensure users only see data relevant to their workspace.
Yes. We provide standard DPAs for all customers and can accommodate custom requirements for enterprise agreements. Contact us to request a copy.
All your data and credentials are retained for 30 days after cancellation, then permanently deleted. Warehouse customers can request a data export before deletion. Live Intelligence customers have no data stored — only encrypted credentials are removed. We provide written confirmation of data destruction.